What is a Data Diode and How Does It Work?
In an era when ransomware attacks can shut down pipelines (as seen with Colonial Pipeline in 2021, costing $4.4 million in ransom) and sophisticated intrusions can disrupt power grids, the question of how to truly isolate critical systems has never been more urgent.
Traditional firewalls and software-based security solutions have their place, but when the stakes involve national security, public safety, or operational continuity, many organisations turn to a more decisive approach: the Data Diode.
In this guide, we’ll explain exactly what a data diode is and how it works, how the underlying technology enforces one-way data flow at the hardware level, and why industries from power generation to defence rely on these devices to protect their most sensitive networks.
Whether you’re evaluating network architecture options or meeting strict regulatory compliance requirements, understanding data diode technology is essential for modern information security.
Key Takeaways
- A data diode guarantees physical, one-way data flow, preventing reverse attacks.
- It is hardware-based, so its security does not rely on configuration or software updates.
- Industries such as energy, defence, healthcare, and finance use data diodes to protect critical infrastructure.
- True data diodes require software integration, such as protocol adapters, to work with modern applications without compromising security.
What is a Data Diode? Understanding Unidirectional Security Technology
A data diode is a hardware-based network appliance that physically enforces unidirectional data flow between two networks. Unlike firewalls or software solutions that rely on rules and configuration, a data diode makes reverse communication physically impossible through its design.
The key purpose is to protect a more sensitive or critical network from attacks originating from less secure network environments. This could mean shielding an operational technology network from enterprise IT threats or preventing unauthorised access to classified data.
Think of it like a one-way valve for network traffic—data flows out through only one direction, but nothing flows back.
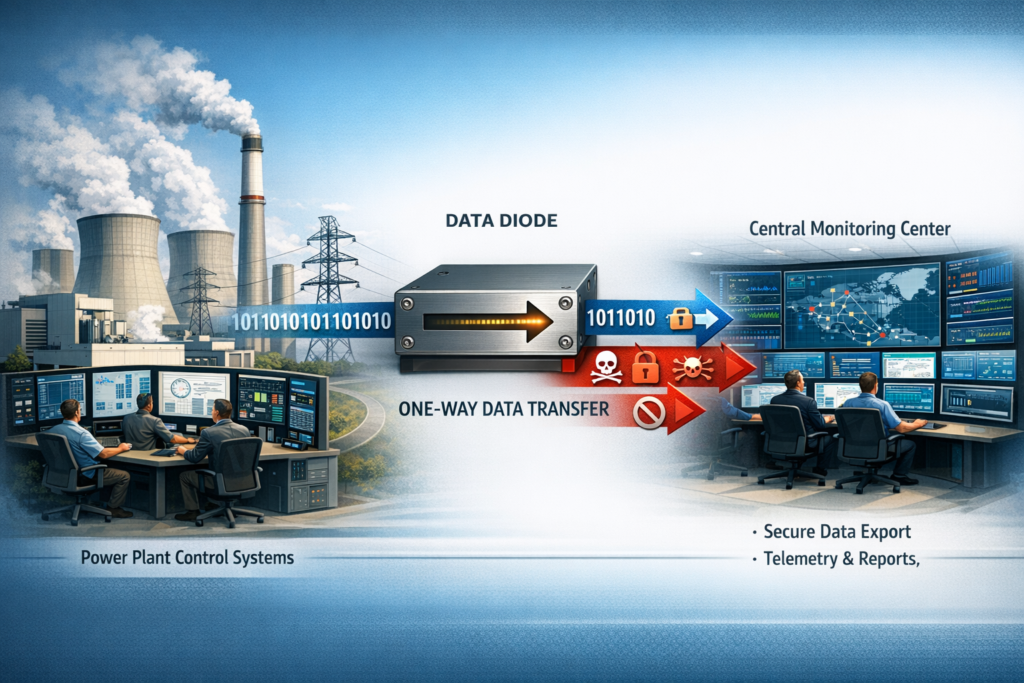
Example: A power generation plant needs to send data to a central monitoring centre for analysis and regulatory compliance reporting. Using a data diode, the plant exports telemetry continuously while making it physically impossible for any commands, malware, or unauthorised access attempts to travel back into the control systems—protecting data integrity and operational technology infrastructure.
A data diode is a specialised cybersecurity appliance designed to guarantee that data travels in only one direction across a network boundary.
You’ll see it referred to as a unidirectional gateway, a unidirectional network device, or a deterministic one-way boundary device in standards documentation from organisations such as NIST and in frameworks such as IEC 62443.
The device is implemented as a hardware-based appliance sitting between two network segments with different trust levels. One side is the “source network” (where data originates), and the other is the destination (where data is received).
Depending on the deployment, the source might be a high-security OT system sending data out, or a less secure network pushing approved updates into a secure network enclave.
The main security benefit: guaranteed isolation. Because the hardware physically cannot receive signals on the sending side, you eliminate entire categories of cyber threats:
- Malware attempting to establish command-and-control channels
- Remote control attacks are trying to send exploit payloads
- Data exfiltration and data leakage attempts through the protected link
- Misconfiguration errors accidentally allow inbound traffic
- Software vulnerabilities that create backdoors in software-based security solutions
This level of assurance is why data diodes are considered the cornerstone of network segmentation strategies in high-security environments, providing unparalleled protection for critical infrastructure.
Unidirectional Data Flow Explained
Unidirectional data flow means information flows in one direction at the physical layer, with no return traffic on the same path. True data diodes achieve one-way data transfer through hardware design, not software rules.
In typical network environments, data flows in both directions. When you visit a website, your computer sends a request, and the server responds. This two-way communication pattern underlies most protocols, including TCP/IP, which expects acknowledgements.
A data diode breaks this pattern entirely. The unidirectional flow deployment looks like:
- Industrial control systems or other critical networks generate data (logs, sensor readings, process metrics)
- The data flows through the diode to an IT network, cloud platform, or monitoring system
- The receiving side processes, analyses, and stores the data
- No packets, commands, or signals can travel back to the source network
This approach maps onto higher-level use cases through software components on each side:
- Log export: SCADA systems sending syslog data to centralized SOC
- Real-time monitoring: Historian databases replicating to enterprise analytics
- One-way data transfer: Transferring production reports without allowing uploads
- Database replication: Software replicates databases from protected networks to reporting servers
Because standard applications expect responses, vendors add protocol adapters and proxy services that terminate the original network connection on one network side and recreate equivalent data flow on the other. This is the protocol break that is essential for making data diodes work with modern software solutions.
How Does a Data Diode Work?
At its core, a data diode relies on physical asymmetry—the hardware cannot function in reverse. This hardware-level enforcement provides secure communication in only one direction.
Physical Implementation
The most common implementation uses fibre-optic technology, providing optical isolation:
Send Module: On the source network side, the appliance contains a network interface with only a transmitter. In fibre-optic implementations, this is typically a laser diode converting electrical signals into light pulses. This module can send data but has no receiver component—literally no hardware capable of accepting incoming signals.
Receive Module: On the destination side, the appliance contains only a receiver (photodiode) that converts incoming light into electrical signals. This module cannot transmit anything because it lacks the hardware to do so.
No Physical Return Path: A single fibre strand runs between these modules from TX to RX. No reverse fibre. No transceiver. No capability for two-way communication. Even if an attacker fully compromises the destination network, they cannot exploit software vulnerabilities to create a backchannel, because the physical path doesn’t exist.
Components are housed in tamper-resistant enclosures, often designed for standard 19-inch rack mounting. Many vendors include tamper-evident seals and secure boot mechanisms to prevent physical modification.
Protocol Break Architecture
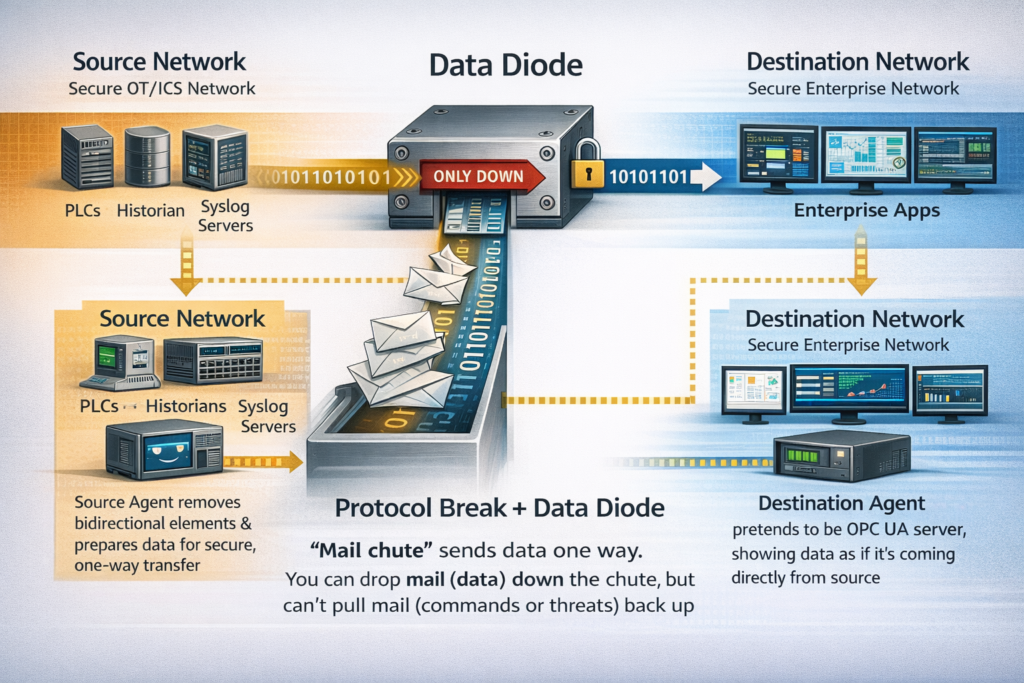
The protocol break makes the device practical for real-world applications:
- A local agent on the source network side collects data from applications (PLCs, historians, databases, syslog servers)
- The agent strips away session state and bidirectional protocol elements
- Data is encapsulated and transmitted through the one direction link
- On the destination side, a corresponding agent receives the stream
- The destination agent emulates protocol servers to local clients, reconstructing data in usable form
For example, replicating an OPC UA data stream: source-side software reads from the OPC server, extracts relevant values, and pushes them through the diode.
On the other side, a proxy server presents itself as an OPC UA server to enterprise applications—even though the actual data source is completely isolated in the secure network.
Think of it like a mail chute in a building:
- You can drop mail down the chute (data going out).
- You cannot pull mail back up (no commands or attacks coming in).
- The mail is repackaged so the recipient can read it like normal mail, even though the source is isolated.
Data Diodes vs. Firewalls and Other Security Solutions
Understanding differences between data diodes and other security solutions is critical for selecting the right tool for your environment.
Security Solutions Comparison
|
Aspect |
Firewall |
Data Diode |
|
Data flow |
Bidirectional (rules-based) |
Unidirectional (hardware level enforced) |
|
Attack surface |
High (complex software, configuration) |
Minimal (no code paths for reverse traffic) |
|
Software vulnerabilities |
Vulnerable to zero-days, patches needed |
Not exploitable for reverse flow |
|
Remote exploitation risk |
Possible via bugs or misconfiguration |
Not possible through one-way data flow |
|
Two-way communication |
Native support |
Physically impossible |
|
Network segmentation approach |
Software policies |
Physical isolation via air gap-like optical isolation |
|
Best fit |
Enterprise networks need interactive access |
Critical infrastructure requiring guaranteed isolation |
|
Computer security posture |
Depends on configuration correctness |
Inherent in the physical nature of hardware |
How Firewalls Work
Firewalls are software-controlled devices that inspect network traffic and apply rules to allow or block specific connections.
They’re fundamentally bidirectional. The hardware can both send and receive packets. Their security posture depends on proper configuration, timely patching of software vulnerabilities, proper administration, and the absence of zero-day exploits.
Firewalls excel at managing general enterprise traffic that requires two-way communication. However, their attack surface is significant in high-risk environments.
Complex rule sets contain errors, firmware harbours exploitable bugs, and misconfiguration creates unintended pathways to sensitive data.
The Data Diode Difference
A data diode cannot be reprogrammed to allow reverse traffic. The hardware’s physical nature makes this impossible. You don’t trust software to enforce the policy. The absence of return hardware is the policy. This enables secure data transfer with unparalleled security guarantees.
Data diodes offer what software-based security solutions cannot: physical proof that no attack can travel back into your critical systems.
In high-security environments such as nuclear facilities and defence networks that protect classified data, regulators often require hardware-based one-way devices rather than software solutions.
Use Cases and Industries Relying on Data Diodes
Data diodes are deployed wherever the consequences of compromise would be severe—measured in terms of public safety, national security, or operational continuity.
Applications by Industry
|
Industry |
Application |
Protected Asset |
Data Types |
|
Industrial Control Systems / SCADA |
Operational technology telemetry export |
Process control networks, SCADA systems |
Real-time sensor data, historian replication, and equipment health |
|
Power Generation & Utilities |
Grid monitoring, NERC CIP compliance |
Transmission control, substation networks |
Telemetry, load balancing data, and safety system logs |
|
Oil & Gas |
Pipeline monitoring, secure transfer to the corporate |
Pipeline control, refinery automation |
Flow rates, pressure sensors, safety interlocks |
|
Defense & Intelligence |
Classified data export, coalition sharing |
Classified networks, command systems |
Intelligence summaries, sensor feeds, operational reports |
|
Financial Services |
Payment processing isolation, data confidentiality |
Transaction systems, settlement networks |
Transaction logs, audit trails, compliance reporting |
|
Healthcare |
Medical device network security, patient data protection |
Surgical equipment, imaging systems |
Device telemetry, patient monitoring data |
|
Manufacturing |
Production data export from air gapped systems |
Factory automation, robotics networks |
Production metrics, quality data, equipment status |
Industrial Control and SCADA Systems
The convergence of operational technology and IT networks created significant security challenges.
Manufacturing plants, power generation facilities, oil and gas pipelines, water treatment systems, and rail signalling networks face the same dilemma:
They need to transfer data to enterprise systems for analytics and compliance, but cannot afford to expose industrial control systems to external threats.
Data diodes enable one-way data transfer of real-time process telemetry, equipment health metrics, production statistics, historian database replication, and safety system logs—all while ensuring that no commands, scripts, or malware can travel back into OT environments via that path. This protects data integrity while enabling secure communication.
Critical Infrastructure Protection
Beyond industrial control, data diodes protect critical infrastructure, including financial services, payment processing, healthcare medical device networks, transportation traffic control, and emergency services dispatch systems.
These sensitive networks require protection against data breaches, data exfiltration, and unauthorised access from external networks.
Real-World Example
Consider a national grid operator managing power transmission. The control network monitors thousands of substations and manages load balancing in real time. Regulators require the operator to share telemetry with national monitoring authorities.
Using a data diode, the operator sends data continuously to the monitoring centre. Analysts observe grid status, detect anomalies, and generate reports. But even if an attacker compromised the monitoring centre completely, they could not send a single packet back into the control network.
A data diode protects national-level data confidentiality and prevents cyber threats from reaching critical networks.
Implementing Data Diodes: Practical Considerations
Successful deployment requires careful planning at both network architecture and application integration levels.
Implementation Steps
Step 1: Define Data Flow Direction
Determine which direction your data must flow:
- OT-to-IT: Exporting telemetry from control systems to enterprise analytics
- IT-to-OT: Importing approved updates into protected systems
- Low-to-high classification: Bringing external network data into secure network enclave
- High-to-low classification: Exporting sanitised reports from classified data networks
Each direction protects different security properties. OT-to-IT primarily protects integrity (no commands return). IT-to-OT primarily protects confidentiality (no data leakage out).
Step 2: Identify Data Types
Document what you need to transfer data:
- Real-time telemetry streams from SCADA systems
- Log files and syslog data
- Database records requiring replication, where software replicates databases
- Document files for archiving
- Video feeds for monitoring
Different data types may require different protocol servers or handling approaches.
Step 3: Position the Diode
Place the diode at clear trust boundaries:
- Between the secure network control network and the DMZ
- Between the classified enclave and the enterprise network
- Between air-gapped systems and external network connectivity
Step 4: Integrate Software Components
Deploy software components, including protocol adapters for specific applications, file transfer proxies, database replication agents for systems that replicate databases, and monitoring tools that provide visibility into operations.
Common Challenges and Mitigations
|
Challenge |
Mitigation Strategy |
|
Legacy protocols requiring ACKs |
Use store-and-forward with local acknowledgement onthe source network |
|
Applications expecting responses |
Deploy protocol servers that emulate services |
|
Configuration change management |
Establish out-of-band procedures for updates |
|
Two-way data interaction needs |
Deploy separate diodes with strict governance (avoid creating a logical bidirectional path) |
Limitations and When to Use Data Diodes
While data diodes offer unparalleled security for their specific purpose, they’re not suitable for every communication pattern.
Inherent Limitations
True data diodes prevent any native two-way communication through the protected link:
- No remote control sessions
- No interactive troubleshooting
- No real-time error reporting without additional mechanisms
- No acknowledgement of received data
If your use case genuinely requires bidirectional access (like remote administration), you’ll need a separate, carefully controlled path—not a data diode.
What Data Diodes Don’t Protect
Data diodes primarily address network-borne threats on the protected path. They don’t replace physical security controls, insider threat programs, endpoint protection, or supply chain validation.
If malicious content is embedded in legitimate data exported through the diode, it can still reach the destination. Content filtering remains important even with one-way data flow.
When Should You Use a Data Diode?
Consider a data diode when:
- You operate critical infrastructure where compromise affects public safety
- National security requirements demand a strong isolation of sensitive data
- Regulatory compliance frameworks require air gap-style controls or network segmentation
- Downtime or system manipulation would have severe financial or operational impacts
- You need to share data with external networks without creating inbound attack paths to sensitive networks
- Software-based security solutions and firewalls provide insufficient assurance for high-risk environments
- Protection of classified data or operational technology from cyber threats is paramount
Data Diode: Hardware-Enforced Security for Critical Systems
A data diode is more than a security device—it’s a physical guarantee that data flows in only one direction. Its hardware-based enforcement removes the risk of cyber attacks travelling back into critical systems, making it essential for:
- Industrial control systems and SCADA networks
- National infrastructure and defense networks
- Healthcare, finance, and manufacturing environments
- Meeting strict regulatory compliance and security standards
The question isn’t whether data diodes are relevant. It’s whether you can afford not to have one protecting your most critical networks.
For organisations looking to safeguard sensitive systems, Allied Solutions can help implement data diode technology to ensure secure, one-way data flow.